Using OpenSSL to verify SSL/TLS connections
OpenSSL is a general-purpose cryptography library and full-featured toolkit for the Transport Layer Security (TLS) and Secure Sockets Layer (SSL) protocols. It’s licensed under the Apache License 2.0, meaning that you are free to get and use it for both commercial and non-commercial purposes, subject to a few simple license conditions. Using OpenSSL to check […]
How To Create a SSH Key

In this tutorial we will explain how you create a SSH Key pair and how to use this key to authenticate on remote devices. SSH, that stands for Secure Shell, is a network protocol used to establish an encrypted connection between two devices. The SSH protocol supports either the use of a username and password […]
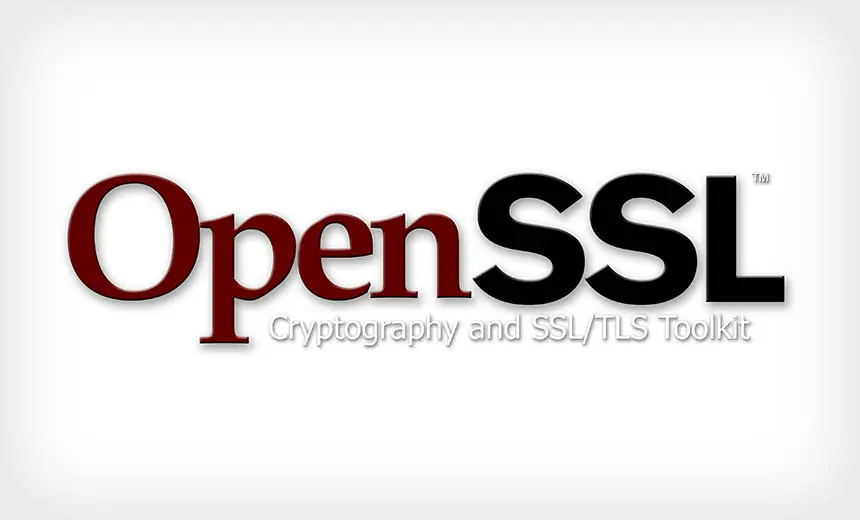
Microsoft blocks Windows Defender ability following major security concerns
Microsoft has blocked the ability to download files using Windows Defender after it was shown how easily it could be used by attackers to install malware onto a computer. Earlier this year, for reasons yet unclear, Microsoft discreetly added the ability to download files using Windows Defender. When this was publicly recognized, there was grave concern from […]
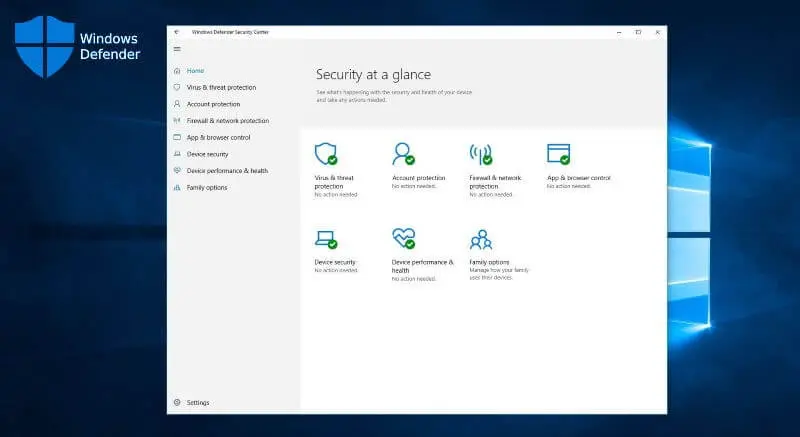
Windows 10 themes can be abused to steal passwords
Security researcher Jimmy Bayne (@bohops) has revealed that specially crafted Windows themes can be used to perform Pass-the-Hash attacks and steal passwords. Pass-the-Hash attacks are used to steal Windows login names and password hashes by tricking the user into accessing a remote SMB share that requires authentication. A theme’s settings are saved under the %AppData%\Microsoft\Windows\Themes folder as a […]
Web security is improving, but so much more to be done

A much-anticipated report from Rapid7, a cybersecurity company based in Boston USA, revealed “frankly shocking” news concerning the current global state of security on the Internet in the wake of the Covid-19 pandemic. According to the massive cross-industry study, completed in the summer of 2020, the findings revealed that despite enormous security problems from the […]
Google’s Android Lockbox spying competitor apps

Revelations have emerged from reported sources that Google is spying on how people interact with rival Android apps. The report mentions how Google is monitoring users interactions with non-Google apps via an internal program and utilizing the data to improve its own products. According to a startling report in The Information, a program called Android Lockbox gives […]
NSA and FBI warn about national security threat due to new Linux malware

The United States the National Security Agency (NSA) and Federal Bureau of Investigation (FBI) have taken the unusual step of publishing a joint security alert containing details about a new strain of Linux malware that the agencies claim was developed and deployed in attacks by Russian military hackers. Through their joint alert, the two agencies […]
Security issues surface as employees use personal computers to Work from Home

The global Covid-19 pandemic forced many businesses to rapidly relocate employees from the office to working from home. For many organizations this meant enacting, and exposing weaknesses, in their emergency plans created to continue business in the event of fire or flood. Most of these back-up plans centered on protecting data and setting up a temporary workplace […]
Work from Home employees ignoring security guidelines

Cybersecurity has always been a big priority in IT but the global pandemic has invoked endless extra headaches for IT managers as remote working became a necessary routine around the world. According to a new study many organizations, despite having good practice and awareness embedded in an office environment, discovered that employees quickly slipped into […]
UPnP vulnerability allows attackers to scan internal networks and steal data

Latest research has revealed that the Universal Plug and Play (UPnP) network protocol has an integral security flaw that leaves printers, routers, and millions of other devices wide open to an attack which can remotely commandeer them. The UPnP protocol has been in use since 2008 predominantly but not exclusively being installed on routers. It allows devices […]